
Leverage a Secure No-code Development Platform
Protect your users and sensitive data. Increase security, privacy, and compliance across the organization with comprehensive security policies and privacy controls, hosted reliably in the EU.
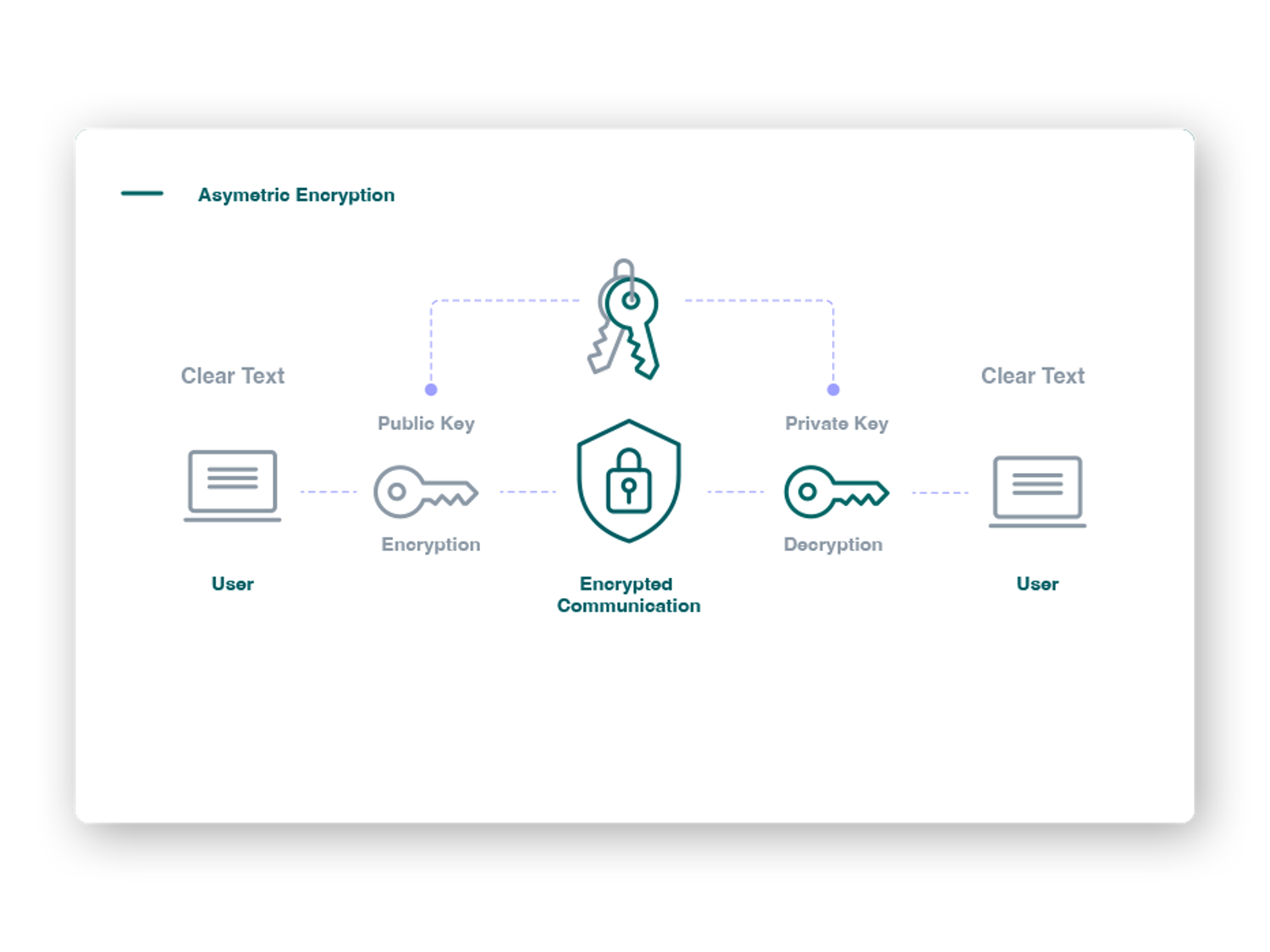
Encryption
Enhance Security
Use encryption to protect sensitive and business-critical data in transit and at rest, and protect your users and applications with built-in multi-factor authentication.
Privacy
Protect Data Integrity
Abide by modern privacy laws by identifying, classifying and anonymizing specific data in your applications and workflows, and use role-based access control to ensure relevant data minimization.
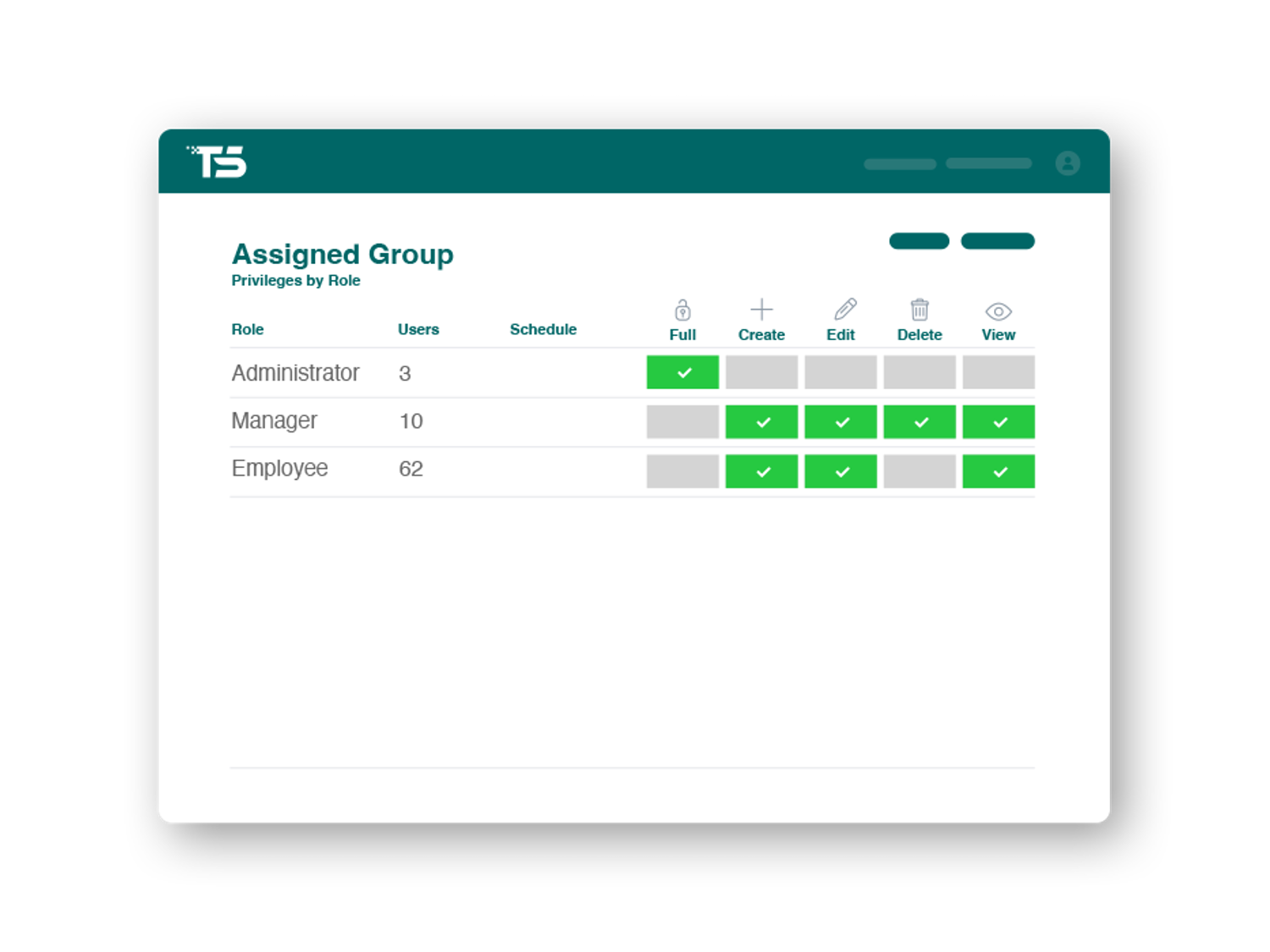
Access Control
Policy-based Access Control
Create policies to define the level of user access based on role, network, location, data ownership, time, authentication method, identity provider and/or group definitions.
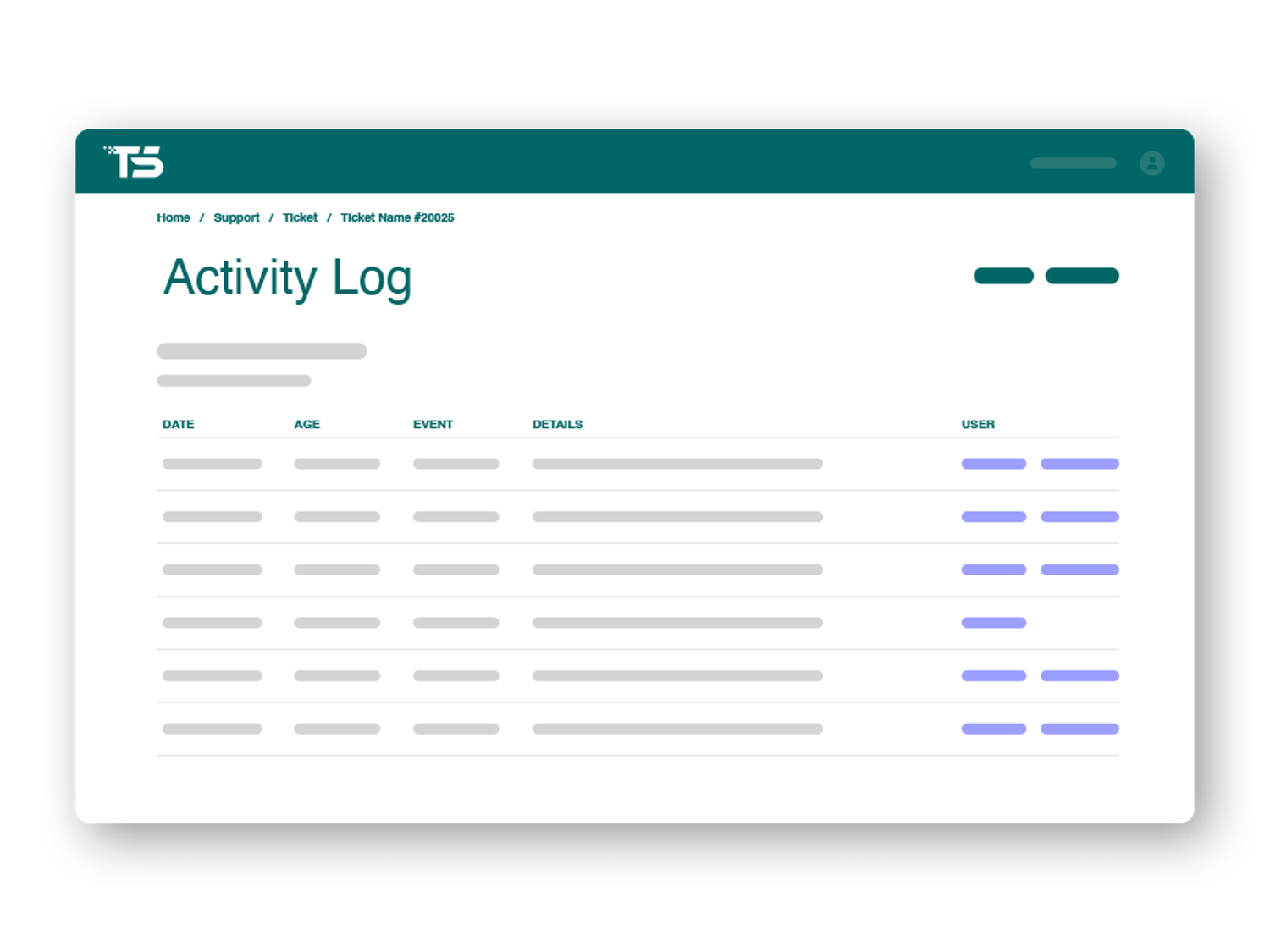
Logging
Activate Logging
Get full visibility into usage, performance and security by turning on; activity, access and revision logging in your applications.
Testimonial
Industry Leaders Take Advantage of Advanced Security
When building applications to support healthcare professionals in one of the most digitalized countries in the world, privacy by design and protection against modern threats become paramount. With TS No-code Platform, we can protect our users, our data, and host it all reliably in the cloud within the EU.
Christian Bonde, CEO, Photologic
Security Features that Scale with Your Needs
Take advantage of policy-based security features to establish the level of protection that fit your purpose, regulatory requirements and the character of your data.
OWASP Level 2
Build applications safe in the notion that they live up to commercially-workable open standard security verification.
Data and file versioning
Easily activate data and file versioning, to generate full logs throughout the lifecycle of structured data, files and documents.
Platform Encryption
Turn on platform encryption to protect your data in transit using TLS and at rest through LUKS AES-256 encryption.
Anonymisation of Data
Analyze and classify your data based on information security principles and anonymise according to modern standards.
Activity Logging
Turn on policy-based activity logging to record any and all user activity in an application. Export log files for documentation purposes.
Field Level Access Control
Control access to data and/or files within an application by adding field and document level security permissions to specific roles.
Status Access Control
Control access to records (data and/or files) within an application depending on the current status. Applies to any user action.